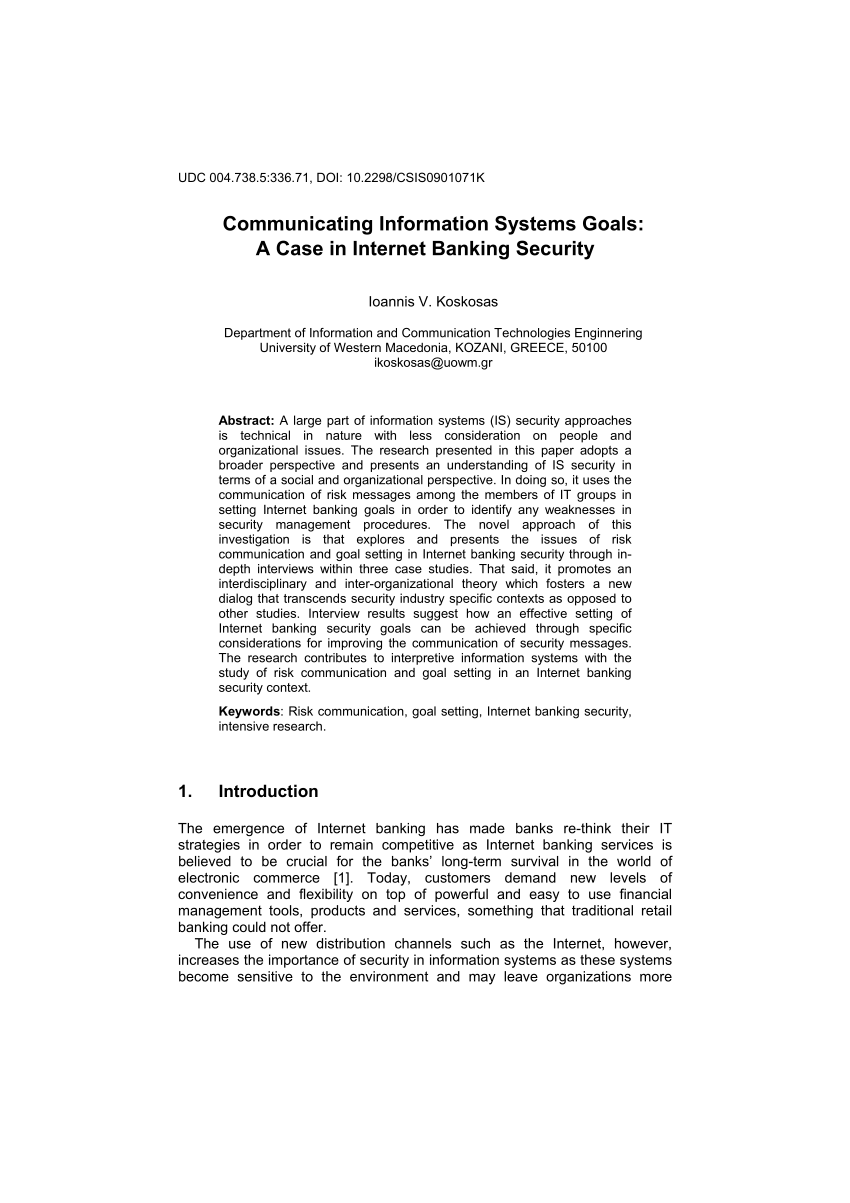
A Socio-Organizational Approach to Information Systems Security Management in the Context of Internet Banking

Application of Soft Systems Methodology (SSM) to develop Information Systems Security Model for Ethiopian Banking Industry

Application of Soft Systems Methodology (SSM) to develop Information Systems Security Model for Ethiopian Banking Industry

PDF) The international journal published by ComSIS Consortium Serbian Academy of Science and Art Mathematical Institute Editorial council Managing board | Dan Simpson - Academia.edu

Project Commitment in the Context of Information Security: Library & Information Science Journal Article | IGI Global

IJRBM - Review of The Literature On The Electronic Banking Adoption Bankers Perspective | PDF | Online Banking | Banks & Banking
![PDF] The Performance Pyramid Framework to Information Systems Security Management Process | Semantic Scholar PDF] The Performance Pyramid Framework to Information Systems Security Management Process | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/980b5ad215649b68e2bb790676ac82c2cdfdfa44/6-Table2-1.png)
PDF] The Performance Pyramid Framework to Information Systems Security Management Process | Semantic Scholar
![PDF] The Performance Pyramid Framework to Information Systems Security Management Process | Semantic Scholar PDF] The Performance Pyramid Framework to Information Systems Security Management Process | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/980b5ad215649b68e2bb790676ac82c2cdfdfa44/3-Figure1-1.png)
PDF] The Performance Pyramid Framework to Information Systems Security Management Process | Semantic Scholar
2004 Association for Computing Machines, Inc. (ACM). This compilation is copyright of ACM. Copyright for components of this w

Encyclopaedia of Information Security Risk Analysis : Disterer, Georg, Koskosas, Ioannis: Amazon.com.be: Books