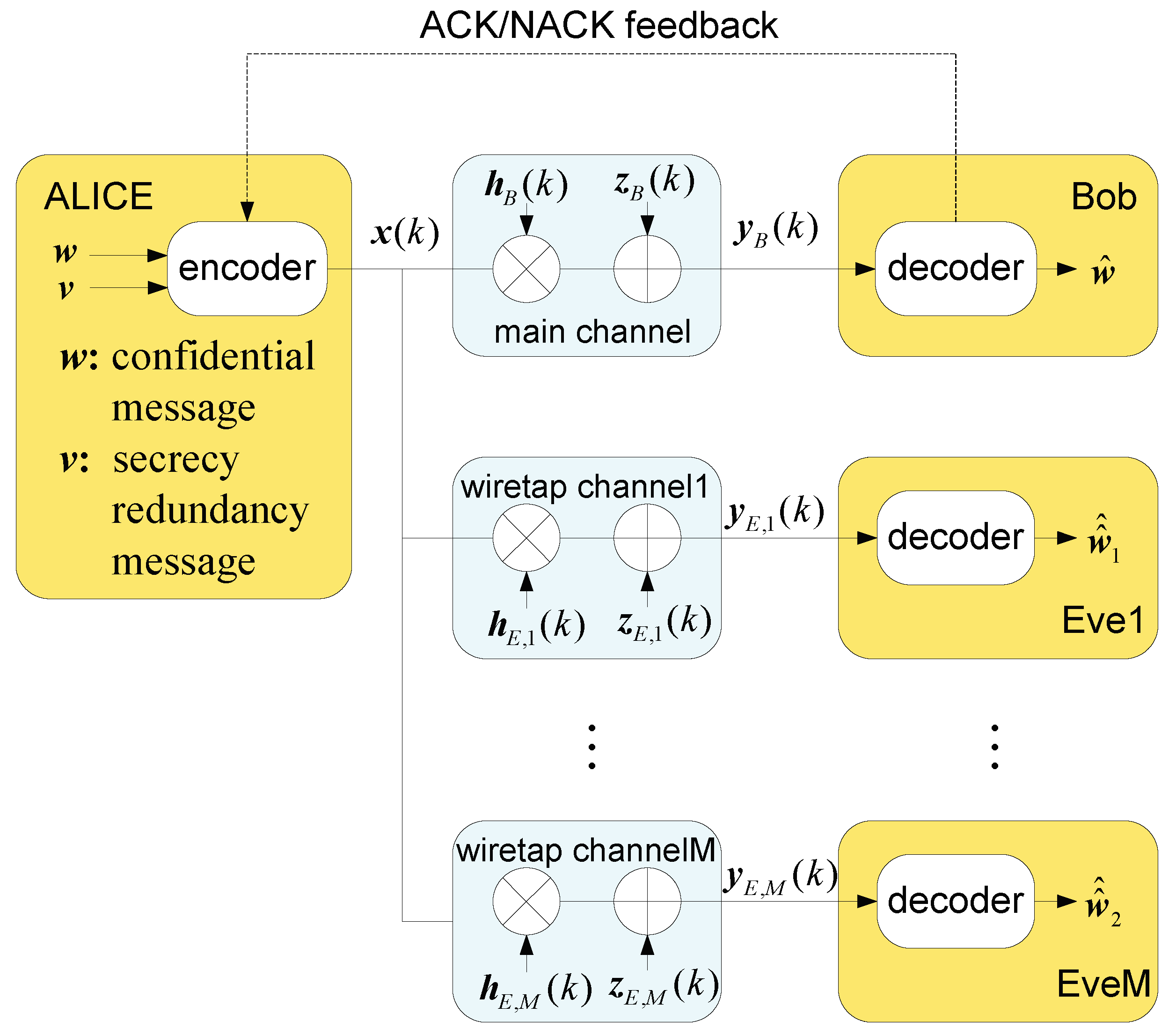
Entropy | Free Full-Text | Rate Adaption for Secure HARQ-CC System with Multiple Eavesdroppers | HTML

Entropy | Free Full-Text | Implications of Coding Layers on Physical-Layer Security: A Secrecy Benefit Approach | HTML

Achieving strong security based on fountain code with coset pre‐coding - Yi - 2014 - IET Communications - Wiley Online Library

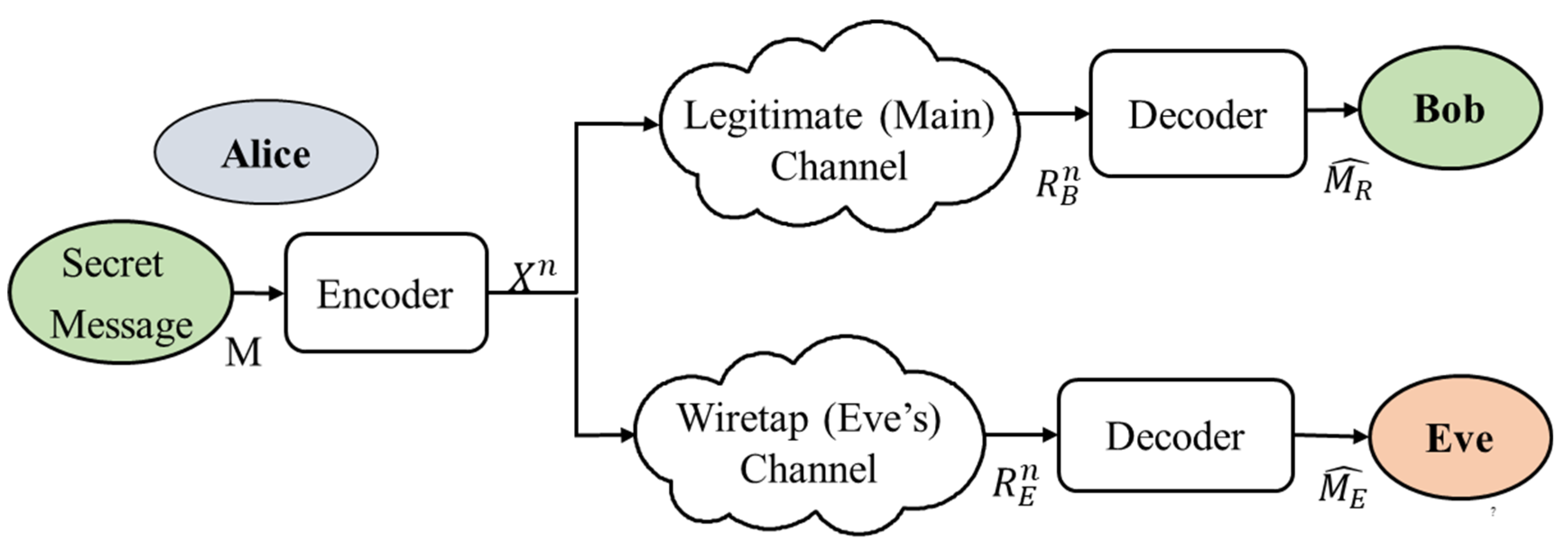
A comprehensive survey of physical layer security over fading channels: Classifications, applications, and challenges - Yadav - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library

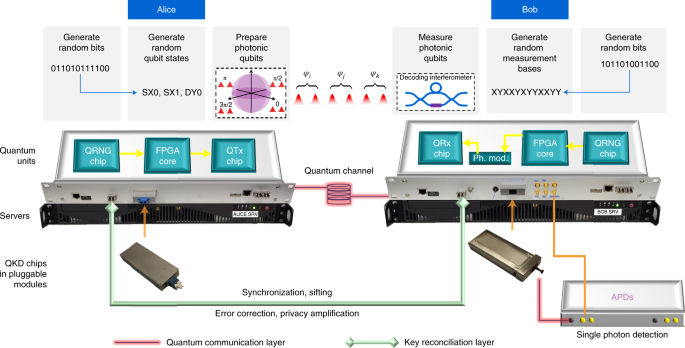
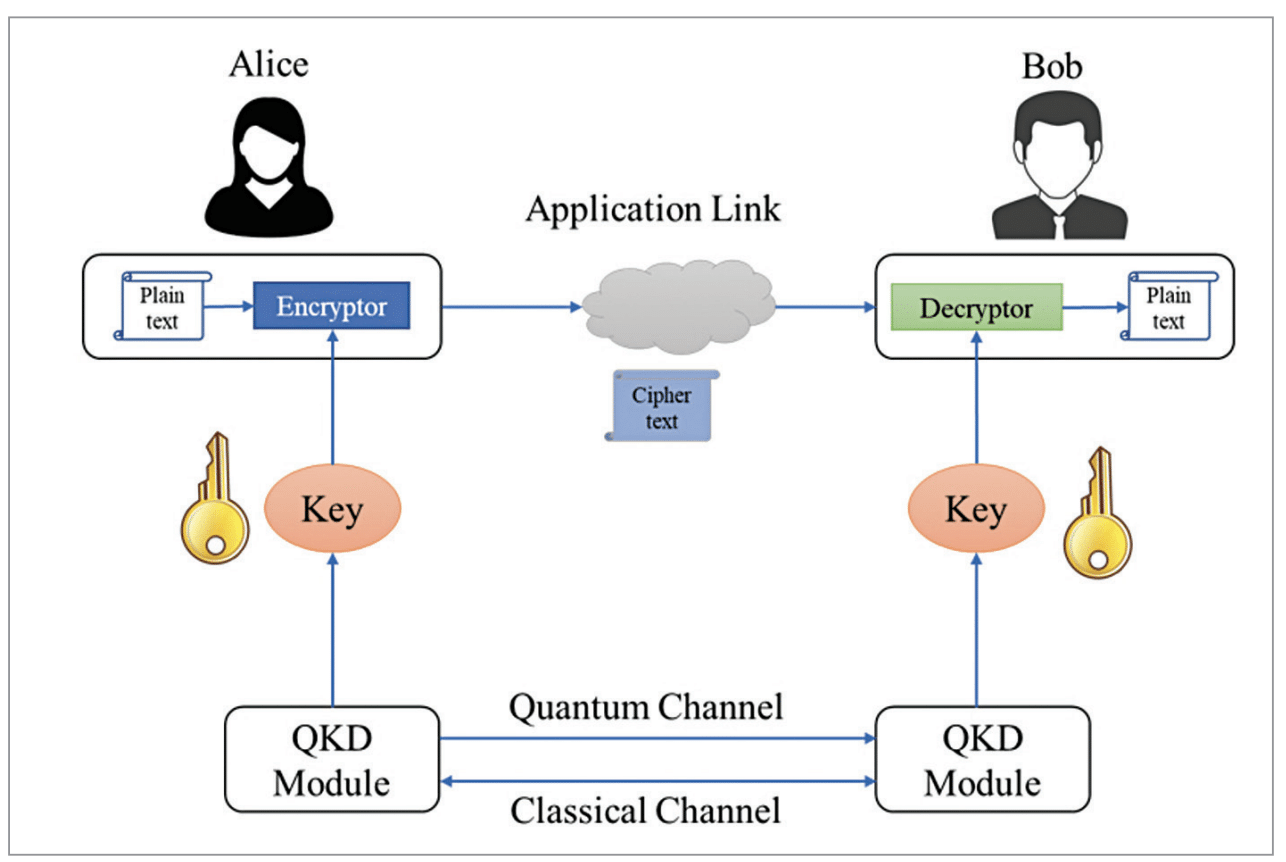
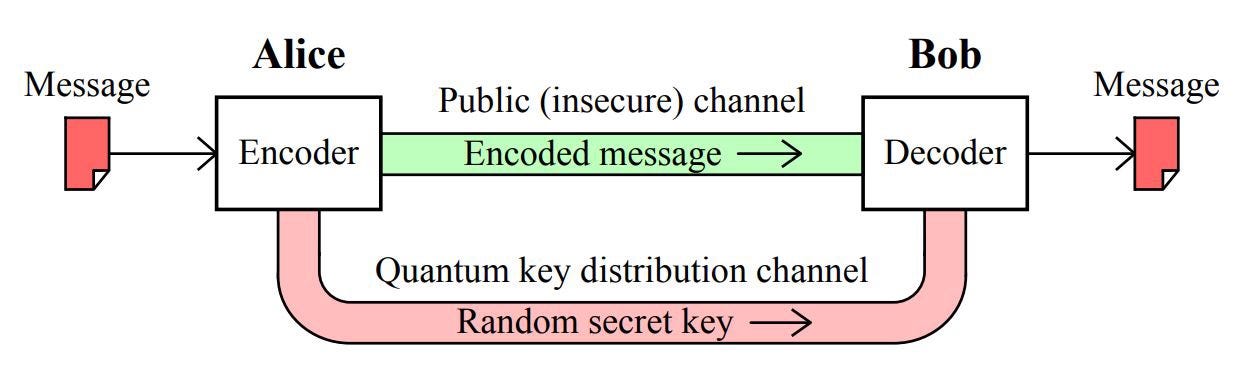
Schematics of LM05 Protocol. Bob prepares the qubit with random bases... | Download Scientific Diagram